MacSync Malware Spreads Through Claude.ai and Replaces Your Crypto Wallet Apps
Want to learn ethical hacking? I built a complete course. Have a look!
Learn penetration testing, web exploitation, network security, and the hacker mindset:
→ Master ethical hacking hands-on
Hacking is not a hobby but a way of life!
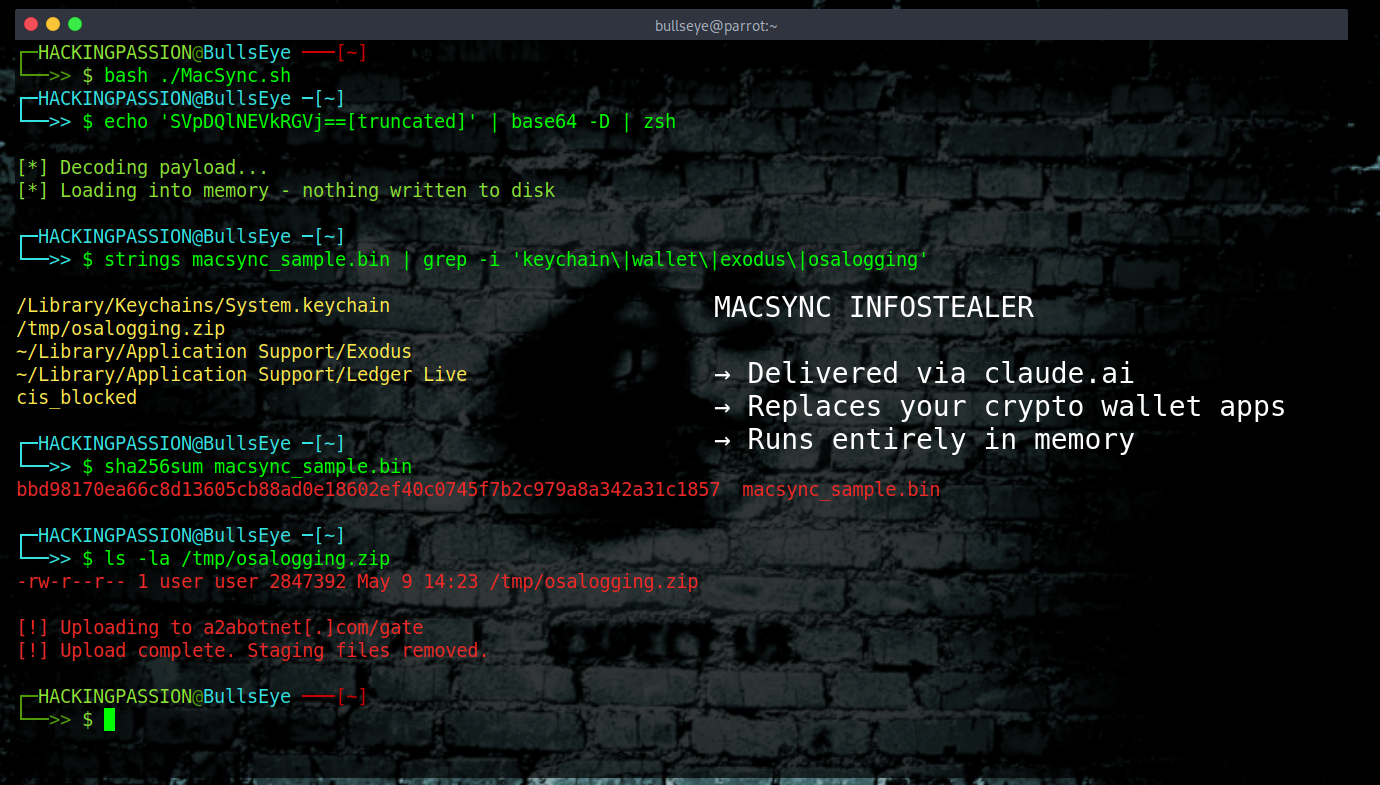
MacSync is spreading through Google ads that lead directly to claude.ai. The installation guide there was written by Claude itself. One Terminal command and the malware is running, your credentials are gone, and your crypto wallet applications have been replaced.
Security researcher Berk Albayrak spotted an active version of this campaign on May 9, 2026 and posted his findings on X. Researcher g0njxa also published findings on X tracing the campaign infrastructure. BleepingComputer independently confirmed a second variant running on completely separate infrastructure.
The campaign goes after developers looking to install Claude Code, Anthropic’s command-line tool for AI-assisted coding. They run Terminal commands as a normal part of their work, trust technical documentation, and their machines are full of things attackers want: API keys, AWS credentials, cloud configuration files, and direct access to live production systems. One compromised machine is worth far more than ten regular laptops.
The attack starts with a Google ad. When someone searches for “Claude download mac” or “install Claude Code,” a sponsored result appears at the top showing claude.ai as the website you’re going to. Google checks that the domain in the ad is real, but not where the link actually sends you. Clicking it takes you to a shared Claude chat, which is a feature that lets anyone publish a conversation publicly under the official claude.ai domain. The guide inside looks exactly like something from an official developer website.
The attackers fed Claude a series of carefully constructed prompts to produce exactly the instructions they needed, with the malicious terminal command embedded in the output. Then they deleted the conversation that showed how they got there, leaving only the finished result. Anyone who opens the link sees a professional installation walkthrough with no trace of how it was made.
At the bottom is a single Terminal command. Terminal is the black screen where you type commands directly into your Mac, no clicking, no buttons. When a command is pasted there and executed, macOS just runs it, no questions asked.
The command uses base64 encoding, which is a standard way of converting any piece of data into a string of letters and numbers that looks like meaningless gibberish to the human eye. It is used legitimately in software development all the time, which is part of why nobody thinks twice about seeing it. Here it hides what the command actually does. When macOS executes it, it decodes itself and immediately reaches out to the attacker’s server to download and run MacSync. The malware loads entirely in memory and never writes itself to disk. Most security tools work by scanning files. A process that exists only in memory leaves them nothing to find.
The server also never sends the same version of the malware twice. Each time the command runs, the server generates a freshly scrambled version of the code before delivering it. This approach is called polymorphic delivery, and it defeats detection tools that rely on recognizing known patterns, because the pattern changes every single time.
Before doing anything else, one variant checks what language the keyboard is set to. If the active input language is Russian or belongs to a country in the former Soviet region, the script exits immediately and sends a single signal back to the server: cis_blocked. The malware filters out entire countries before it even starts.
Once running, MacSync targets specific locations on the machine:
- → The macOS Keychain, the system’s built-in storage vault for passwords, certificates, Wi-Fi credentials, and secure notes
- → Saved passwords, session cookies, and autofill data from all major Chromium and Firefox-based browsers
- → Cryptocurrency wallet private keys and seed phrases
- → AWS and Kubernetes configuration files, the authentication files developers use to access cloud infrastructure
- → Shell command history and detailed system metadata
MacSync goes further than most infostealers when it finds Exodus, Ledger Live, or Trezor Suite installed. Rather than just stealing the wallet data, it downloads a replacement core file from the attacker’s server and overwrites the legitimate application. The wallet continues running and looks completely normal. Every seed phrase and private key entered after that point goes directly to the attacker. Uninstalling MacSync afterwards does not fix this, because the wallet application itself has been swapped out.
Everything collected gets compressed into an archive at /tmp/osalogging.zip and sent to the attacker’s server using a standard HTTP request, the same type of request your browser makes when loading any webpage. The malware pretends to be a regular browser so the traffic blends in. If the upload fails, the malware retries up to eight times with increasing gaps between each attempt, specifically built to get the data out even on an unreliable connection. After a successful upload, all staging files are removed from the machine.
MacSync started as a stealer called Mac.c, first seen in April 2025 and built by a developer using the online alias “mentalpositive.” Researchers tracking the development found signs pointing to Russian origin, which fits with the CIS language filter built into the malware itself. In cybersecurity, attribution is one of the hardest problems. Code gets copied between groups, infrastructure gets reused, and language markers in code can be planted deliberately. What the indicators point to is a direction, not a confirmed identity. Mac.c was cheap by design and sold on underground forums as a cheap alternative to better-known Mac stealers. Within months, new operators purchased the project when it risked dying from lack of time and funding. The original developers stayed on, a persistent backdoor component built in Go was added, which is a programming language that compiles into small self-contained files that run quietly in the background, and it relaunched as MacSync. It now operates as a Malware-as-a-Service, meaning any criminal can rent access to the builder and delivery infrastructure for a low monthly fee with no technical knowledge required.
Claude is not the first AI platform used as a delivery channel this way. In early December 2025, a Huntress customer searched “how to clear disk space on macOS,” clicked a sponsored Google result, and landed on a ChatGPT conversation offering helpful cleanup steps. Those steps installed the AMOS infostealer. Huntress found the same poisoned content running on Grok as well, and confirmed the attack reproduced across multiple search queries including “clear system data on iMac” and “free up storage on Mac.” Kaspersky documented a related campaign simultaneously, using a fake OpenAI Atlas browser on ChatGPT as bait. Claude is the third major AI platform weaponized this way in five months.
The first Claude-specific campaign was documented by Moonlock Lab, the research division of MacPaw, on February 11, 2026. Two variants were running at the same time. To get the ads approved, the attackers had compromised the verified Google Ads accounts of two legitimate organizations: Earth Rangers, a Canadian children’s charity, and TSQ SA, a Colombian watch retailer. Because both accounts had real histories and solid reputations with Google, the malicious ads sailed through Google’s checks without raising any flags. The guide was titled “macOS Secure Command Execution” and was viewed more than 15,600 times before it came down. That is a view count, not a confirmed infection number. Ad-blocking company AdGuard had independently counted 12,300 views before Moonlock published their findings. When the Claude artifacts were taken down, the operation shifted to Squarespace-hosted pages within hours while keeping the same ads running. Someone is actively managing this infrastructure.
In March 2026, Oasis Security found three separate vulnerabilities in Claude.ai that chain together into an attack pipeline they named Claudy Day.
The first was that invisible HTML tags embedded in a URL parameter could pre-fill the Claude chat box with hidden instructions. The person sees one message. Claude processes something additional that is completely hidden from view. The second was that Claude’s built-in code runner is allowed to talk to Anthropic’s own servers, so an attacker who embeds their API key in those hidden instructions can tell Claude to search the victim’s conversation history and quietly upload the results to attacker-controlled storage. The third was an open redirect on claude.com where any link in the format claude.com/redirect/ followed by a destination would forward a visitor to any external address without warning. Because Google Ads checks the hostname and not where the click actually goes, an attacker could run an ad showing claude.com as the URL while sending visitors anywhere they wanted.
Anthropic patched the prompt injection vulnerability after Oasis reported all three through responsible disclosure. The other two issues are currently being addressed.
Security firm 7AI found a Windows version of the operation and named the full campaign Claude Fraud. A fake extension for VS Code appeared on Microsoft’s extension marketplace disguised as the official Claude Code plugin. VS Code is the code editor most developers use to write software, and extensions can do a lot on your machine. Installing the fake extension triggered PowerShell in the background, with PowerShell being Windows’ built-in scripting engine for automating system tasks. The malware used it to tell Windows Defender to stop watching certain folders, then pulled down a second payload called CrossMark2. Three confirmed infections were found in company networks that were actively monitored.
At the end of March 2026, Apple added a Terminal warning to macOS Tahoe 26.4 that stops a suspicious command from running the moment you paste it and shows a message explaining that scammers routinely distribute malicious instructions through websites, apps, and support chats. Less than two weeks after the feature shipped, Jamf found that attackers had already found a way around it. A new variant uses the applescript:// URL scheme, which opens Script Editor directly from the browser. Script Editor is another macOS tool that can execute code. Because the command never goes through Terminal, the new warning never triggers. The specific campaign Jamf documented delivered the AMOS infostealer rather than MacSync, but the bypass technique works for any ClickFix payload.
If you recently ran a Terminal command from a source you’re not completely sure about, these signals are worth checking:
- → Unexpected osascript processes running as child processes of
curl,zsh, orbash. Osascript is macOS’s built-in scripting engine and is what MacSync uses to access the Keychain and browser data - → The pattern
echo | base64 -D | zshappearing in Terminal history - → The file
/tmp/osalogging.ziphaving been created or recently modified - → Unusual outbound connections from Terminal to unfamiliar domains
- → Gaps in
~/.zsh_historythat do not match normal activity
| |
| |
Change every password saved in a browser or in the Keychain on any potentially affected machine. SentinelOne and Moonlock Lab have both published YARA rules and indicators of compromise for hunting related variants.
The Terminal warning in macOS Tahoe 26.4 is a step forward, but the Script Editor bypass shows that the operating system alone won’t keep you safe. The only thing that actually works is knowing what a command does before running it. A shared Claude chat, a ChatGPT conversation, a GitHub README, a page labelled Apple Support, none of those sources make a command safe to run. The name on the page says nothing about whether the content is safe. For software downloads, go directly to the official website rather than clicking any search result, sponsored or otherwise.
How social engineering bypasses technical defenses, how malware evades detection, how credentials get collected and sent out, and how attackers exploit trusted platforms is exactly what the ethical hacking course covers step by step:
Hacking is not a hobby but a way of life. 🎯
Sources: Moonlock Lab | Oasis Security | 7AI Threat Research
→ Stay updated!
Get the latest posts in your inbox every week. Ethical hacking, security news, tutorials, and everything that catches my attention. If that sounds useful, drop your email below.