Fiber Optic Cables Turned Into Hidden Microphones
Want to learn ethical hacking? I built a complete course. Have a look!
Learn penetration testing, web exploitation, network security, and the hacker mindset:
→ Master ethical hacking hands-on
(The link supports me directly as your instructor!)
Hacking is not a hobby but a way of life!
Fiber optic cables running through your walls can be turned into hidden microphones that record every word spoken in the room. This is not a theory anymore. Researchers from Hong Kong Polytechnic University published a fully working attack at the NDSS Symposium in February 2026, and the results are going to change the way a lot of people think about what is running through their walls. 😏
I refused to get fiber optic internet installed at my house. Call it a security instinct. Everyone around me thought I was being paranoid. Turns out that feeling was right.
A fiber optic cable is a thin strand of glass that carries data as pulses of light, and for decades that made fiber the secure choice. Copper wire leaks electrical signals out of the cable in all directions, and those signals can be picked up from the outside without ever touching the wire. Fiber carries light, not electricity, so there is nothing leaking out, nothing to pick up, no signal escaping the glass. That assumption held for a long time.
It no longer holds.
When sound moves through a room and reaches a glass fiber, it causes tiny physical bends in the cable. The sound pushes against the glass, barely, almost too small to measure, but enough. Those tiny bends slightly change how the laser light travels through the fiber, and that change carries information. That information can be turned back into audio.
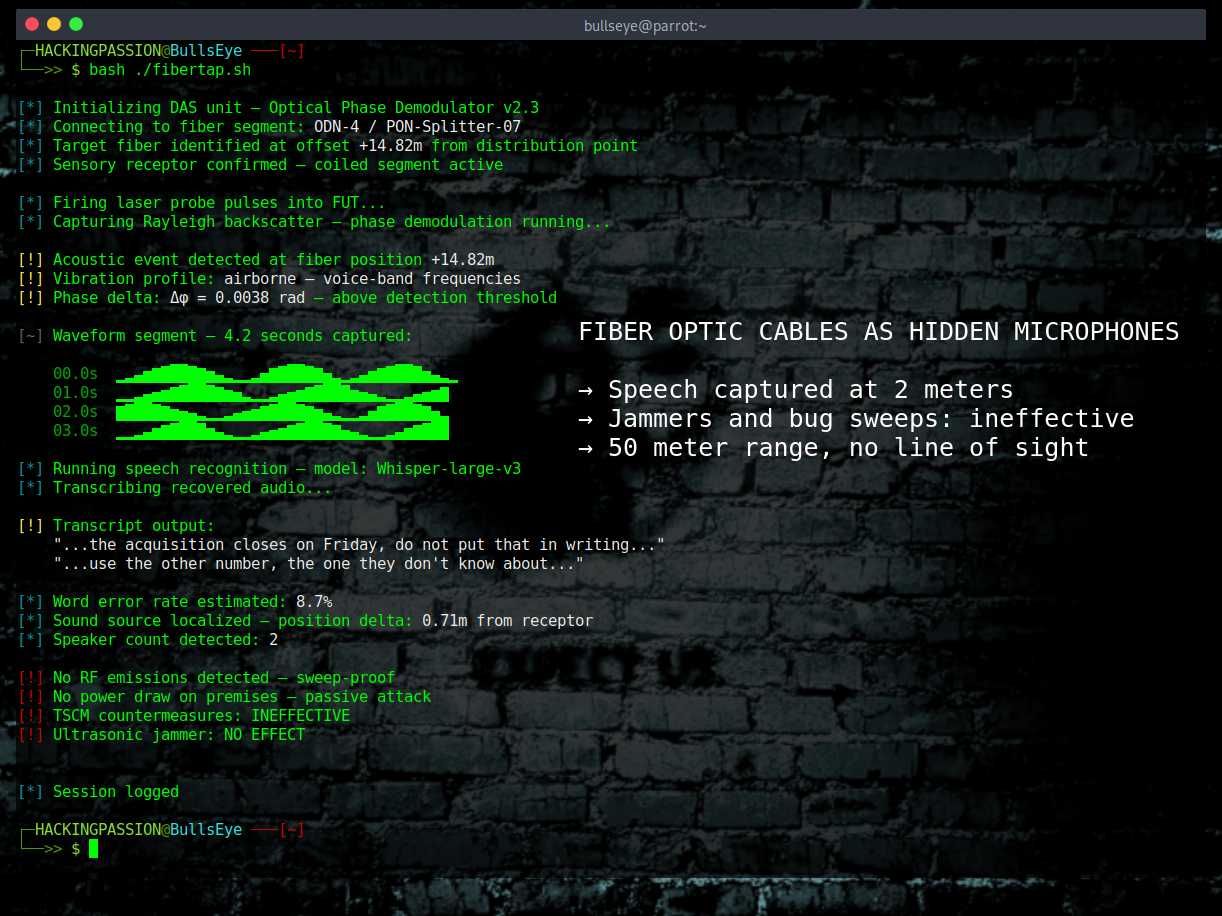
The technology that does this is called Distributed Acoustic Sensing, or DAS. DAS was originally built for things like pipeline monitoring, border security, and earthquake research. It works by firing laser pulses down a fiber and reading the light that bounces back. Think of it like radar, but for vibrations along the entire length of the cable at the same time. Any change in that returning light reveals exactly what is happening at that point along the cable, accurate down to the centimeter. Connect a commercial DAS unit to the far end of a home fiber connection and the cable inside the building becomes the microphone.
The problem is that a standard fiber cable running straight along a wall does not pick up voices very well. Footsteps travel through the floor and the cable catches those just fine, but speech moves through air and by the time that pressure reaches the glass it is too weak to read clearly. The researchers solved this with something they call a sensory receptor.
Fifteen meters of standard fiber cable, wound tightly around a hollow plastic cylinder, 65mm wide, made from the same material as a regular plastic water bottle. That coiled cylinder catches incoming sound and turns it into a stretching and pulling force along the entire length of wound fiber at once, which is a clever physics trick: instead of one tiny spot on the cable bending slightly, the whole coil responds at the same time, which makes the signal strong enough to read. Place that cylinder inside the standard plastic wall box that sits on the wall after every home fiber installation, and from the outside it looks completely normal. From the inside, it is a listening device.
In real office testing at 2 meters from a conversation, the system picked up over 80% of what was said. At 1 meter, fewer than 10 words out of every 100 were missed. The AI tools used to turn the audio into text, Nvidia’s Parakeet and OpenAI’s Whisper, had no trouble with the rest. The person running this attack can be 50 meters away, in a different room or outside the building, with no view of the target space at all.
To understand how wide the attack surface actually is: there are over 500 million active fiber-to-the-home connections worldwide right now. China alone accounts for more than 60% of that. Twenty-one countries have already crossed 50% household penetration, with the UAE sitting at 99.5%, South Korea at 96.6%, and Singapore at 87.5%. This is not a niche installation in a handful of cities. Half the world already has this cable in the walls.
Now here is what none of the other coverage on this research is mentioning.
Most fiber installations do not pull a single cable into a building. Several are laid at once, because once the walls are open and the conduits are in place it makes sense to run a few extra while the work is being done. One cable goes active, the rest stay unused inside the walls, ceilings, and cable runs throughout the building. These are called dark fibers, and they belong to no active service, are checked by nobody, and run right through the rooms where private conversations happen every day. Someone with access to the fiber cabinet on the street, the one that feeds the whole building, does not need to touch the active internet connection at all. Those dark fibers are already sitting in the walls, completely unguarded.
People who take privacy seriously sometimes buy ultrasonic jammers to block hidden microphones. These work by filling the room with high-pitched sound that scrambles the electronics inside a standard microphone and makes recording impossible. Against this attack, they do absolutely nothing. The sensory receptor has no electronics in it at all, nothing to scramble, nothing to overload, nothing that responds to ultrasound in any way. The researchers tested this directly and found zero effect on the quality of what was captured even with a jammer sitting right next to the receptor.
Professional bug sweeps, the scans that security companies run through boardrooms and government offices to find hidden listening devices, also miss this completely. Those sweeps look for radio signals that a hidden device sends out. Glass fiber carrying light sends out nothing, and a sensory receptor sitting inside a standard wall box leaves no electronic trace of any kind. No wireless signal, no power draw, no radio frequency of any kind. It is plastic and glass, on a wall, looking exactly like every other fiber box in the building.
And it is not only listening. With three receptors placed around a room, the system can figure out exactly where in the room the sound is coming from, with an average error of only 77 centimeters. It tracks movement. It can also recognize what is happening in the room just from the fiber signal alone, footsteps, someone typing on a keyboard, a washing machine running, all of it, without a microphone anywhere in the picture.
The best setup in the study had the fiber wall box attached to the underside of a desk. When the box sits against the desk surface, the vibrations from the tabletop travel straight into the fiber through solid material instead of through air, which cuts out most of the signal loss. In that setup the system got fewer than 9 words wrong out of every 100, which is cleaner than most phone calls.
The real limitation of this attack is that it needs someone to physically get to the fiber box inside the building to install the receptor, and someone to get to the street cabinet that feeds the building. That is not something that can be done remotely. But every fiber installation in the world involves a technician going inside and opening that box. So does every service visit, every upgrade, every reported fault. The researchers point to corrupt ISP employees, subcontractors, and people pretending to be telecom technicians as the realistic ways this access gets obtained, and they reference documented cases of all three.
The DAS equipment costs several thousand to tens of thousands of dollars, which puts this firmly in the territory of government operations and serious corporate espionage, not everyday crime. Law firms with sensitive cases, executive offices, research companies with valuable technology, diplomatic buildings. Exactly the places that already pay for professional security sweeps, and exactly the places those sweeps will not catch this.
Tapping fiber at the big infrastructure level is not new. Operation Ivy Bells in 1971 was a joint US Navy, CIA, and NSA mission that used divers to attach a recording device to a Soviet underwater military communications cable. The NSA program RAMPART-A, running since 1992, tapped fiber traffic at the major network hubs where international cables converge. The USS Jimmy Carter, a nuclear submarine, was reportedly built with a special 100-foot hull extension specifically to support non-invasive taps on undersea fiber cables. The Snowden documents showed that GCHQ was pulling data from the undersea fiber cable landing points in the UK and sharing it with the NSA.
What this 2026 research changes is the distance. The attack moved from the backbone of the global internet to the last 10 meters inside a building.
Here is what actually reduces the risk.
→ Do not leave excess fiber coiled up inside the wall box. Installers often do this to keep things tidy, but every extra loop is more cable that can pick up sound. Ask that any leftover length gets routed back outside the room instead.
→ Keep fiber cables running flat and straight through rooms where privacy matters. A cable looped around anything, a cable tie, a hook, a piece of furniture, picks up sound much better than a straight run does.
→ Put sound-absorbing material on walls in rooms where sensitive conversations happen. Sound that never reaches the cable cannot be picked up from it.
→ For high-security spaces, look into optical isolators on the fiber line. These are simple passive components that only let light travel one way through the cable, which stops the returning light signal that DAS needs from getting back to the attacker’s equipment.
→ The physical box on the wall matters. Lock it, keep a record of what is inside it, and watch anyone who opens it.
→ Check who has access to the fiber cabinet that serves the building. If that cabinet is not properly secured, the risk exists no matter what is done inside the walls.
The paper is titled “Hiding an Ear in Plain Sight” and was presented at NDSS 2026 by researchers from Hong Kong Polytechnic University and the Chinese University of Hong Kong.
The social engineering angle that makes this attack possible, understanding how attackers get physical access by impersonating legitimate technicians, is exactly the kind of thinking covered in my ethical hacking course.
(The link supports me directly as your instructor!)
Hacking is not a hobby but a way of life.
Source: NDSS Symposium 2026
→ Stay updated!
Get the latest posts in your inbox every week. Ethical hacking, security news, tutorials, and everything that catches my attention. If that sounds useful, drop your email below.